In a perfect world, all of your vendor partnerships would automatically be safe and easy to navigate. Unfortunately, in reality, even the most diligent and conscientious vendors introduce some elements of risk into your organization. Luckily, the trusty vendor risk assessment enables you to identify potential pitfalls and proactively protect your organization.
As a procurement professional, you know better than most the importance of properly vetting vendors. Beyond simply selecting the right one based on their experience, pricing and capabilities, you must also carefully consider what might go wrong. Indeed, the vendor risk assessment is procurement’s way of imagining, considering, avoiding and preparing for various worst case scenarios involving supplier partners.
In this blog, we’ll focus on the ins and outs of the vendor risk assessment. To begin, we’ll define what a vendor risk assessment is, why it’s important and when to use one. Next, we’ll walk through how to create and issue an assessment. Finally, we’ll provide several examples and templates to help you get started.
- Vendor risk assessment basics
- How to create and use a vendor risk assessment
- Sample vendor risk assessments: Templates you can use
Vendor risk assessment basics
What is a vendor risk assessment?
A vendor risk assessment is a questionnaire used to identify and evaluate the liability associated with buying goods and services from third parties.
Vendor risk assessments are sometimes shortened to VRA and may also be called a supplier risk assessment, third-party risk assessment or vendor survey. Regardless of what it’s called, the purpose of the questionnaire is to uncover and evaluate risks introduced by partnering with a vendor or supplier.
To really understand vendor risk, it’s important to keep in mind a few things
- Risk is simply the possibility of a negative outcome, not the certainty of one. In some cases, the threat associated with an identified risk may never materialize.
- When determining what to do about risk, you’ll need to evaluate the probability of the risk materializing as well as the potential impact if it does.
- The presence of risk doesn’t necessarily doom the vendor partnership. As with all things procurement, vendor risk is a constant balancing act. Does the possibility of a negative outcome outweigh the value the vendor delivers?
- Your organization’s appetite for risk is unique. As you evaluate the results of a vendor risk assessment, let your goals decide how your organization approaches and mitigates risk.
The importance of evaluating vendor risk
No organization (even your own) is entirely free of risk. Luckily, a vendor risk assessment represents the first step in successful vendor risk management. Indeed, risk management is a continuous process that includes identifying vendor risk using regular assessments, evaluating the results with a risk matrix and then determining how to move forward.
In some cases, the risk uncovered may be minor enough not to warrant any action. On the other hand, significant risk may prevent a vendor partnership from moving forward due to the likelihood or impact of the risk occurring.
For example, unrecognized or unmitigated vendor risk can lead to data breaches, service disruption, reputation damage, regulatory fines, lost revenue and lawsuits. Ideally, conducting a risk assessment helps your organization plan to avoid, minimize or neutralize consequences when a risk materializes.
The impact of vendor risk
The effort to combat vendor risk is constant, even for large, global organizations. These are just a few examples of recent vendor-related incidents at well-known companies.
- VW says data breach at vendor impacted 3.3 million people
- Car makers will lose $100B in 2021 due to semiconductor shortage
- At Gap Inc., shareholder value still trumps worker safety
- Salesforce says a ‘major issue’ with its cloud service results in outage for some customers
When to use a vendor risk assessment
Risk is ever present. So, to properly manage it, you’ll need to issue vendor risk assessments periodically.
During the RFP process
Sometimes the best way to manage risk is to avoid it all together. Consequently, the vendor risk assessment should be a regular part of your RFP process.
Generally, we recommend sending the initial vendor survey near the end of your RFx process when you’ve arrived at a short list of vendors or a preferred vendor. By sending the survey later in the process, you avoid making extra work for the vendors that aren’t a fit. However, take care to send and evaluate it before you finalize the partnership because the results may impact your contracting process.
To explore the RFP process in more detail, download the ebook: The RFP process guide.
Throughout the vendor lifecycle
After your initial assessment, it’s important to check back in and regularly evaluate risk. With established vendors, the frequency of updates should depend on the vendor’s importance to your organization as well as the probability of the risk occurring.
For example, a data center vendor that hosts your customer-facing application may complete a quarterly vendor risk assessment. On the other hand, your janitorial service provider may only need to update their risk assessment once a year.
When a risk event occurs
Ideally, issuing regular vendor risk assessments will help you avoid negative outcomes altogether. Sadly, the unfortunate reality is that some risks will come to fruition. When that happens, it’s important to issue a fresh supplier risk assessment. Ideally, the new assessment will identify what measures to implement to make sure the issue doesn’t arise again.
How to create and use a vendor risk assessment
1. Determine what types of vendor risk to explore
The goal of the document is to identify any areas of concern which can span a variety of topics. While it’s common for vendor risk assessments to cover data security or regulatory compliance, they can be used to explore much more.
Common considerations in a vendor risk assessment
- Data security – Are they equipped to protect your customers’ data as well as your own?
- IT infrastructure – Can they support your needs now and if you need to scale?
- Financial stability – Will they be solvent for the foreseeable future?
- Regulatory compliance – Do they follow local, state and federal laws?
- Litigation – Are there current legal matters pending?
- Reputation – Could the vendor’s public perception negatively impact your reputation?
- Performance – Will the vendor be able to meet your expectations?
- Upstream stability – Does the vendor have reliable access to the materials they need to supply your business?
- Downstream stability – Is the vendor stable enough to withstand an economic downturn?
- Operations – Does the vendor use effective processes, documentation and mitigation policies?
- Geographic factors – Could operations be interrupted by natural disasters, infrastructure problems or political unrest?
- Strategic exposure – Are your ideas and trade secrets safe? Does the company work with your competitors?
The topics covered by your vendor risk assessment will vary based on the needs of your business as well as the type of vendor. For instance, you likely don’t need to go into great detail on data security with your office coffee supplier who won’t interact with customer information.
2. Write your vendor risk assessment questions
Once you’ve determined which considerations to include, you’re ready to write questions. While it may seem daunting, it doesn’t have to be. Fortunately, you can reference a sample risk assessment and see common questions.
Also worth noting, if you use RFP management software, you can create a risk assessment template to simplify the process. Furthermore you can use the software to set up reminders and issue your recurring assessments digitally. By centralizing the vendor risk assessment process, you can avoid back and forth emails and difficult to locate files. Afterall, the last thing you need when facing a crisis is to spend precious time trying to find a vendor’s risk assessment records.
Sample vendor risk assessment questions
Data security
- Who in your organization manages data security?
- What policies and processes are in place to ensure data security?
- Do you outsource network or security services and how often are penetration tests performed?
- What data security certifications does your organization hold?
IT infrastructure
- Describe your hardware configurations and backup procedures.
- What is your process for data recovery?
- In the event of a breach or interruption of service, what is your communication process?
- What technology do you use to monitor the health and security of your data centers?
Financial stability
- Describe your ownership structure and/or funding.
- Can you provide recent financial statements?
- What liability coverage do you hold and at what limits?
Regulatory compliance
- What regulations are you subject to and can you provide proof of compliance?
- How do you verify ongoing compliance with licencing and regulatory requirements?
Litigation
- Are there current legal matters pending against or involving the company?
- Have you been a party to any recent employee actions?
Performance
- Can you provide recent customer references?
- What percentage of projects are delivered on time and within budget?
- Describe your project management processes and documentation.
- What technology do you use to collaborate and communicate with customers?
Upstream stability
- Do you perform due diligence or vendor risk assessments for your supplier partners?
- Have any historical vendor supply issues impacted your ability to serve customers?
Geographic factors
- Do you have a preparedness strategy for human-caused or natural disasters?
- What policies are in place to minimize disruption in the event of a wide-spread disease outbreak?
Strategic exposure
- Do you currently work with any of our key competitors?
- What confidentiality policies do you have in place to protect our intellectual property?
3. Determine a course of action
When you get responses back from your vendors, it’s time to evaluate the results. Generally, suppliers are familiar with the vendor risk assessment and have already addressed many of the most common concerns. Luckily, that means that the majority of the assessment requires no further action on your part.
However, there will inevitably be some answers that are less than ideal and must be evaluated. Often, a vendor risk assessment matrix or vendor risk matrix helps assess the threat level.
Vendor risk assessment matrix
The risk matrix enables you to evaluate threats based on their probability and impact. Then, with the resulting risk level, you can determine what to do next.
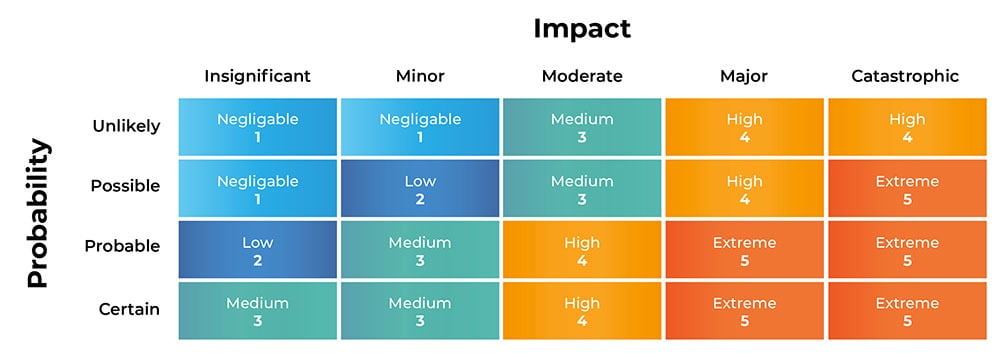
1. Negligible risk: No action required
Risks that have a negligible rating typically don’t require any action. Not only are they mostly unlikely to occur, but the impact is small enough that neutralizing the threat is quick and takes little effort.
2. Low risk: Simply be aware
Low risk threats have minimal impact on your business. Indeed, they may cause some temporary inconvenience but they won’t interrupt your ability to deliver. They don’t require any proactive action, but awareness of the issue alone helps to reduce the likelihood of it happening.
3. Medium risk: Mitigate to minimize
For risks with some impact and likelihood, the best course of action is to address the gap. Basically, this type of risk can be solved with proactively adjusted policies, processes and procedures. Even if it seems like the issue is entirely solved, it’s still important to regularly review to ensure successful mitigation.
4. High risk: Mitigate and plan
Even if you identify a moderate risk, the vendor may deliver enough value or a critical service that justifies the engagement. In this case, you may need to take steps to proactively and continually mitigate. Additionally, because of the likelihood and level of threat, you’ll want to prepare an action plan to minimize potential damage.
3. Extreme: Avoid entirely if possible
While rare, in some cases, the risk a vendor introduces is simply too high to justify. Unfortunately, this probably means you should go back to the drawing board and find an alternate vendor.
Sample vendor risk assessments: Templates you can use
Each of these vendor risk assessment templates are a little different, focusing on a variety of issues. They are helpful, easy to navigate, ready to be customized. Draw inspiration from them, or customize them to meet your needs.
Digital vendor risk assessment template – SafetyCulture
Rates topics ranging from operational procedure to references. It can be completed digitally or downloaded as a PDF.
Created in a joint effort by the CISA’s Information and Communications Technology and Supply Chain Risk Management task force, this third-party risk assessment is extensive. Indeed, the document spans 47 pages and covers a wide range of important topics. It’s a great resource to help you build your own third-party risk assessment.
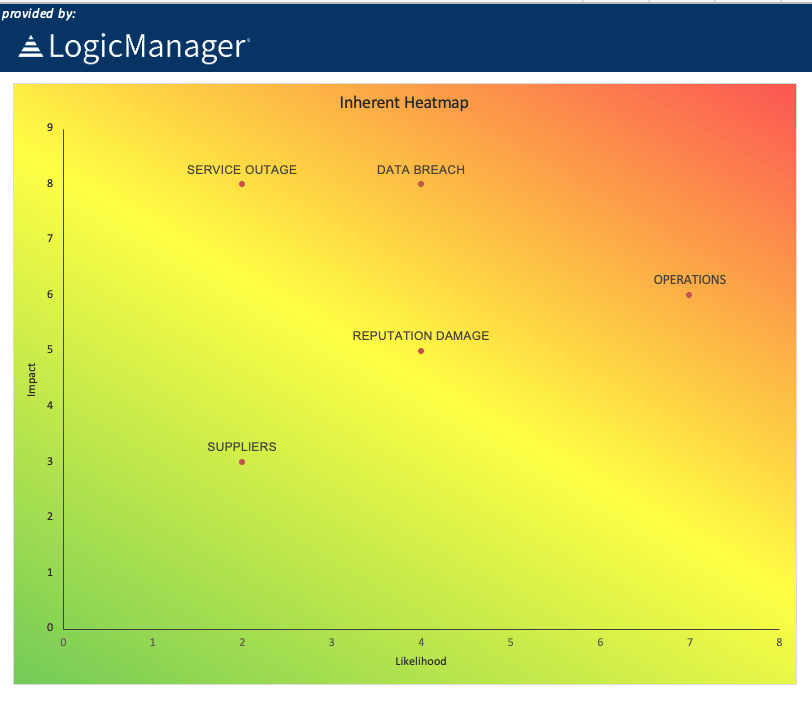
Supplier risk assessment template – LogicManager
Entirely customizable, this template is best used to evaluate the responses from your vendors. It helpfully has categories that identify the risk, what could go wrong, impact and likelihood. In addition, the template takes it one step further to create a visual risk map on a secondary tab.
Sample vendor risk assessment questionnaire – Smartsheet
This Excel vendor risk assessment focuses specifically on information technology. Indeed, it covers data center security, web application security, infrastructure protection, security controls and more.
When you engage with a new vendor, you want to ensure they understand your needs and can deliver innovation and value. However, it’s just as important to make sure that they don’t introduce unnecessary or unacceptable risk to your business.
Ultimately, you want to follow that old piece of advice: trust, but verify. Luckily, the vendor risk assessment is the best, most reliable way for you to do that and protect your organization.